What is Email Phishing? A Basic Overview
What is Phishing?
Phishing is a very pesky cyber attack method that started in the mid-90s. It is a type of online scam where attackers rely on impersonation to trick unsuspecting victims into providing sensitive personal information, installing malware onto their device through bad links, or worse - relinquishing your company's vital information.
There are many variations of phishing, but for the sake of this article we'll focus primarily on Email phishing.
How does Email Phishing work?
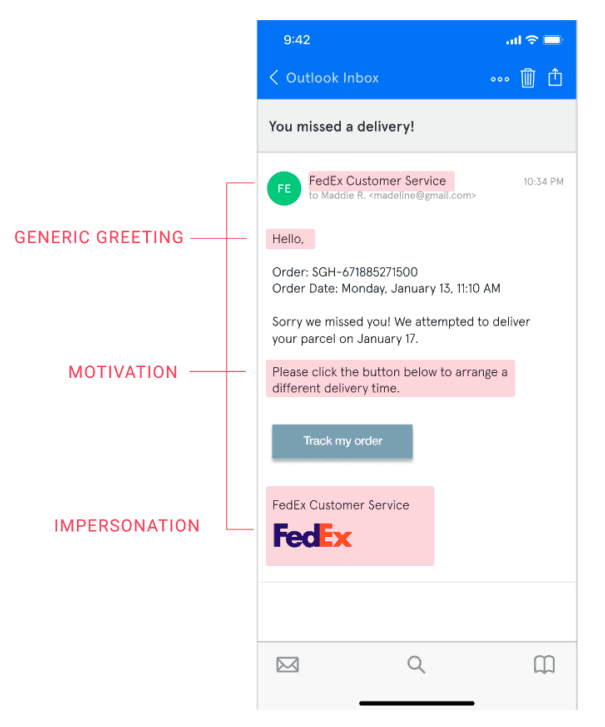
It's pretty simple, really. The basic premise is that an attacker sends an email pretending to be a trusted company and invites you to click on a link. That link will go to a phony look-alike page of the company where any information provided will go directly to the attacker - such as usernames, passwords, account numbers, etc. Once the victim has entered this information, the attacker can do with it what he pleases. Let's take a look at an example email:
How to Spot a Phishing Attempt
In the above email example, you may notice a few red flags
- The "generic greeting" doesn't use your full name. More often than not, trusted companies will send a personalized greeting.
- The sender is Maddie R from [email protected]. This should be the biggest red flag because the emails should come from @fedex.com (or something similar).
- The "Order" and "Order Date" doesn't really add up. Some critical thinking on your behalf will help you realize that FedEx doesn't know what you ordered or when. They're a third party. Red flag!
What is The Goal of Phishing?
The reasons for phishing vary widely. Some entities are motivated for financial gain, while others have used these tactics to embarrass celebrities. You may remember in 2014, where someone used a phishing technique to trick celebrities into providing their iCloud credentials. Thus, leading to a large-scale dump of private photos from many famous celebrities including Kate Upton, Jennifer Lawrence, and Emma Watson.
Below is a list of Phishing Statistics that we thought were interesting from 2019:
Top Five Types of Data That Is Compromised
- Credentials (pin numbers, passwords, login information)
- Personal Information (address, full name, phone number)
- Internal Data (employee information, company secrets)
- Medical (insurance information, treatments)
- Bank (credit card numbers, account numbers)
Symantec's Top 5 Subject Lines for Phishing Emails
- Urgent
- Request
- Important
- Payment
- Attention
Top 10 Most Impersonated Brands
- Apple
- Netflix
- Yahoo
- PayPal
- Chase
- Microsoft
- eBay
- Amazon
Sources
This article serves as a brief overview of Email Phishing. If you are interested to learn more, we recommend starting your journey with one of the links below:
- https://www.zdnet.com/article/what-is-phishing-how-to-protect-yourself-from-scam-emails-and-more
- https://www.tessian.com/blog/phishing-statistics-2020
- https://www.tessian.com/blog/phishing-vs-spear-phishing
- https://www.csoonline.com/article/2117843/what-is-phishing-how-this-cyber-attack-works-and-how-to-prevent-it.html
- https://www.csoonline.com/article/3153707/top-cybersecurity-facts-figures-and-statistics.html
- https://securityboulevard.com/2020/04/phishing-statistics-the-29-latest-phishing-stats-to-know-in-2020