Data Centers can be Easy Picks for Terror
Physical Infrastructure
On the subject of Cybersecurity and Critical Infrastructure Protection, the most important aspect of a data center's security is where the critical hardware is being housed. Data centers across the world are very similar in physical infrastructure to that of any other industrial building. They are being supported by HVAC systems, fire safety systems, lighting control systems, power supply, etc. The most vulnerable of which is the HVAC system.
If you want to take down a data center you don't need to penetrate the network, you don't need to inject a virus, you don't need passwords, you don't need access, you don't need to take a grid and standby power – simply turn off the air conditioning and the servers will stop themselves. If the rooftop units were damaged the center could be shut for days at the very least. According to Andrey Nikishin, head of future technologies projects at Kaspersky Lab, "It's easier to take down a data center by damaging the cooling system than by attacking each of its servers."

A simple drone could cost
a company millions of dollars.
If it has an IP address, it can be hacked and needs to be secured. You can slap an IP address on anything these days. Data center infrastructure is no exception, and it makes subcontracting support of data center infrastructure like HVAC, security cameras, and power management more compelling.
Mike JordanSenior DirectorThe Sante Fe Group
DDoS Attacks
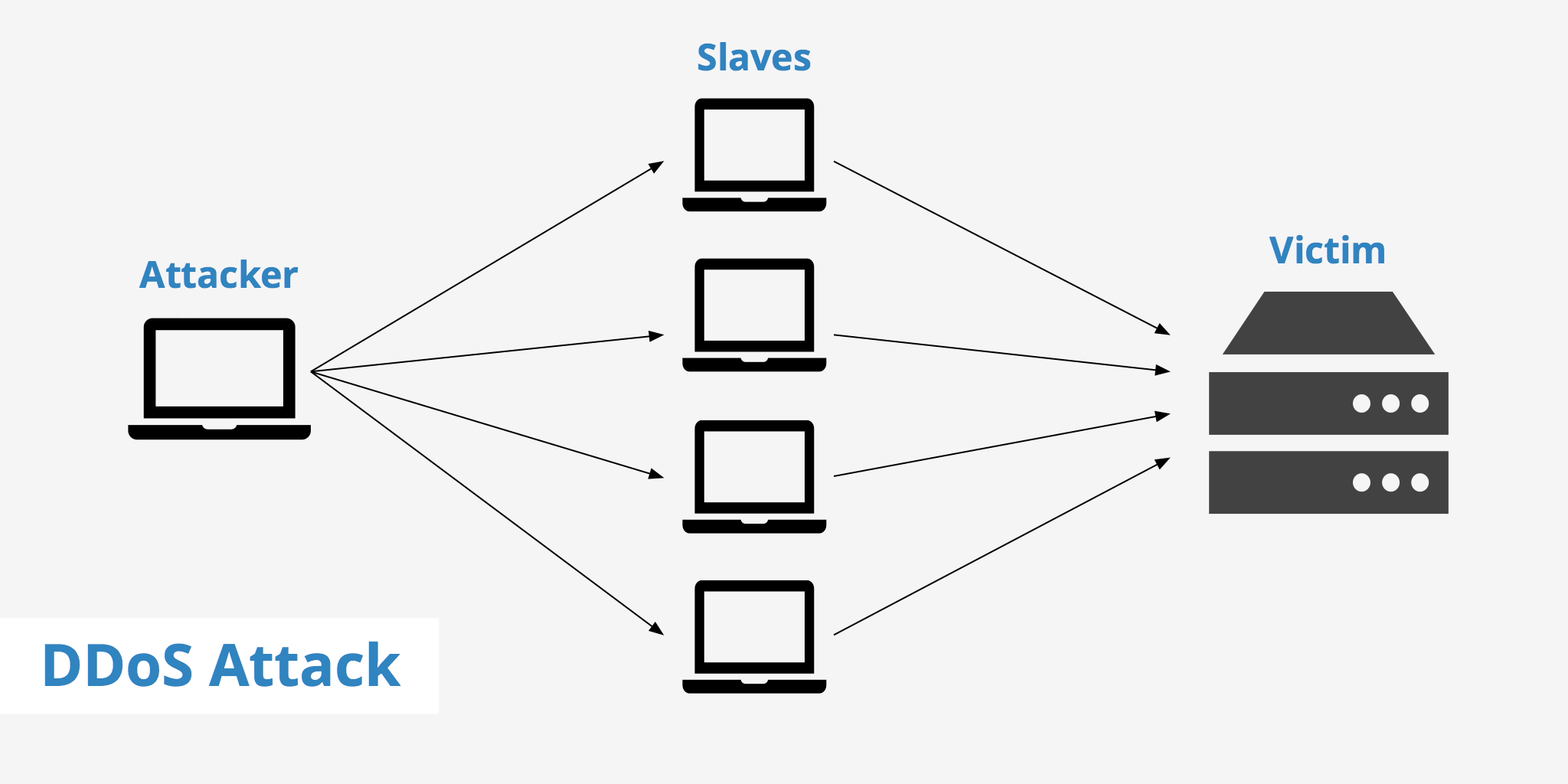
A DDoS (Designated Denial of Service) can be carried out fairly easily. It requires an attacker to gain remote control of a network of online machines, known as a 'botnet,' by infecting IoT and network devices with malware. With a botnet established, an attacker has the ability to direct the machines to work together and flood the targeted IP with requests. Their goal is to cause the targeted network or server to overflow capacity, resulting in denial-of-service to normal traffic. (Note: There are several other types of DDoS attacks as well, for an in-depth list of attacks, check out this article)
According to a Benchmark study by the Ponemon Institute, "Cybercrime represents the fastest growing cause of data center outages, rising from 2 percent of outages in 2010 to 22 percent in 2016". This has grown in 2019 as well, due to the ease at which hacktivists and bad actors can obtain DDoS tools, kits, and services. DDoS ready-to-go kits can be bought online, and even YouTubers and others label themsevles as "stressors" and "booters." They're available on freelancer website and hacking websites, and are willing to sell their services to anyone.
Source: keycdn.com
In order to understand the costs of DDoS attacks on Data Centers, let's look at the key findings from the Kaspersky-B2B "IT Security Risks Survey 2017" :
- As an average, the cost of a DDoS attack for enterprises was $2 million. For a small or mid-size business, the average cost was $120,000.
- 33% of those surveyed cited the costs of fighting a DDoS attack and restoring services as the main burden associated with DDoS attacks, and 25% said money spent investing in an offline or back-up system while online services are unavailable was the primary burden.
- 23% said a loss of revenue and business opportunities occurred as a direct result of a DDoS attack, and 22% listed the loss of reputation among clients and partners as a direct consequence of a DDoS attack.
Internet of Things (IoT) Attacks
According to Symantec's 2019 Threat Report, "Routers and connected cameras make up 90 percent of infected devices, almost every IoT device is vulnerable, from smart light bulbs to voice assistants." IoT devices are soft entry points and commonly targeted by attackers. If an attacker gains control of an IoT device, they can destroy or wipe it, intercept SCADA communications, and steal credentials and data.
Due to the sheer volume of personal data that the Internet of Things brings to data centers, many ethical concerns are being raised. If your Apple watch broadcasts your location, heart rate, stored data (such as where your home is located) - to what people assume is a private network - what would happen if the wrong people got ahold of that information? Every time an IoT device is used, some information is getting stored on the 'cloud' and can be vulnerable to attacks. While this may not be an attack directly on the data center, peripheral damage is still a major liability.

Source: Macstories
References:
- https://www.datacenterknowledge.com/security/data-center-infrastructure-often-overlooked-security-risk
- https://www.pymnts.com/news/security-and-risk/2018/kaspersky-data-indicates-the-global-cost-of-ddos-is-going-up/
- https://www.msspalert.com/cybersecurity-research/kaspersky-lab-study-average-cost-of-enterprise-ddos-attack-totals-2m/
- https://www.cloudflare.com/learning/ddos/what-is-a-ddos-attack/
- https://fardapaper.ir/mohavaha/uploads/2018/03/Fardapaper-The-Internet-of-Things-IoT-Applications-investments-and-challenges-for-enterprises.pdf

